Switch Your Linux Servers To Public Key Authentication
Public Key Authentication
I have been told through the years to always do this, but I've always had to research how every time. I've had trouble finding an end-to-end tutorial so I wind up needing to search out all of the parts. I have put together the path I take the shortest route to get this accomplished and secure my servers. I don't know about you, but my severs are constantly getting hit by bots trying to break in through the sshd password. I sometimes like to watch auth.log and pretend it's my apache access.log so that I had traffic.
This is important! Doing this in the wrong order, or not knowing what you're doing can lock you out of your server. I've done it. It's unpleasant. I have a step that assures this works before you loose you connection.
Client Computer
My client computers are MacBooks, and the remote server is Ubuntu. If you have Windows then you're out of luck with this tutorial. If this makes you mad, contact me, I'll update it :)
First thing is to open up a terminal window and log into your remote server using the password. This is your backup window so if things go South, you can undo your config changes!

I like to tail the syslog to see if any bots try to log in in the process. This terminal keep open in the background as your backup.
Next, you need a key. On your client computer (mac) open up another terminal window and cd to the /Users/YourName/.ssh folder. You can use the key that already exists, but since I have multiple servers, I like to create a key for each server. Follow these commands to create your key:
$ ssh-keygen -t rsa
This command will create the key asking the name of the key. It offers the example /Users/YourName/.ssh/id_rsa, but if you have one you may not want to overwrite it. Create a name, lets say "remoteserver".
You have the option to add a passphrase which is a password to the key if you want yet another layer of security. Once your key is created, we can ship it straight to the server with this:
# ssh-copy-id -i ~/.ssh/remoteserver yourname@remoteserver.com
Next, I like to add a block to my local ssh config so that I can simplify the login process. Since I use different key names, I'd have to log in using the -i flag, but I want to bypass this. Access the file .ssh/config and add a block like this replacing your data:

At this point, you want to test and make sure you can login without using a password. You can try this with:
$ ssh remoteserver
That should just log you in without requiring a password. Yay! You're halfway there!
Remote Server
At this point you should have two terminal windows open and SSHed into the remote server. If not, you should open another and log in so you have a backup open. I can't say it enough. I'm currently on Ubuntu 19.10, but I'm pretty sure most debian flavored distros will have this in the same place (use vim or vi or however you like to edit text files server side):
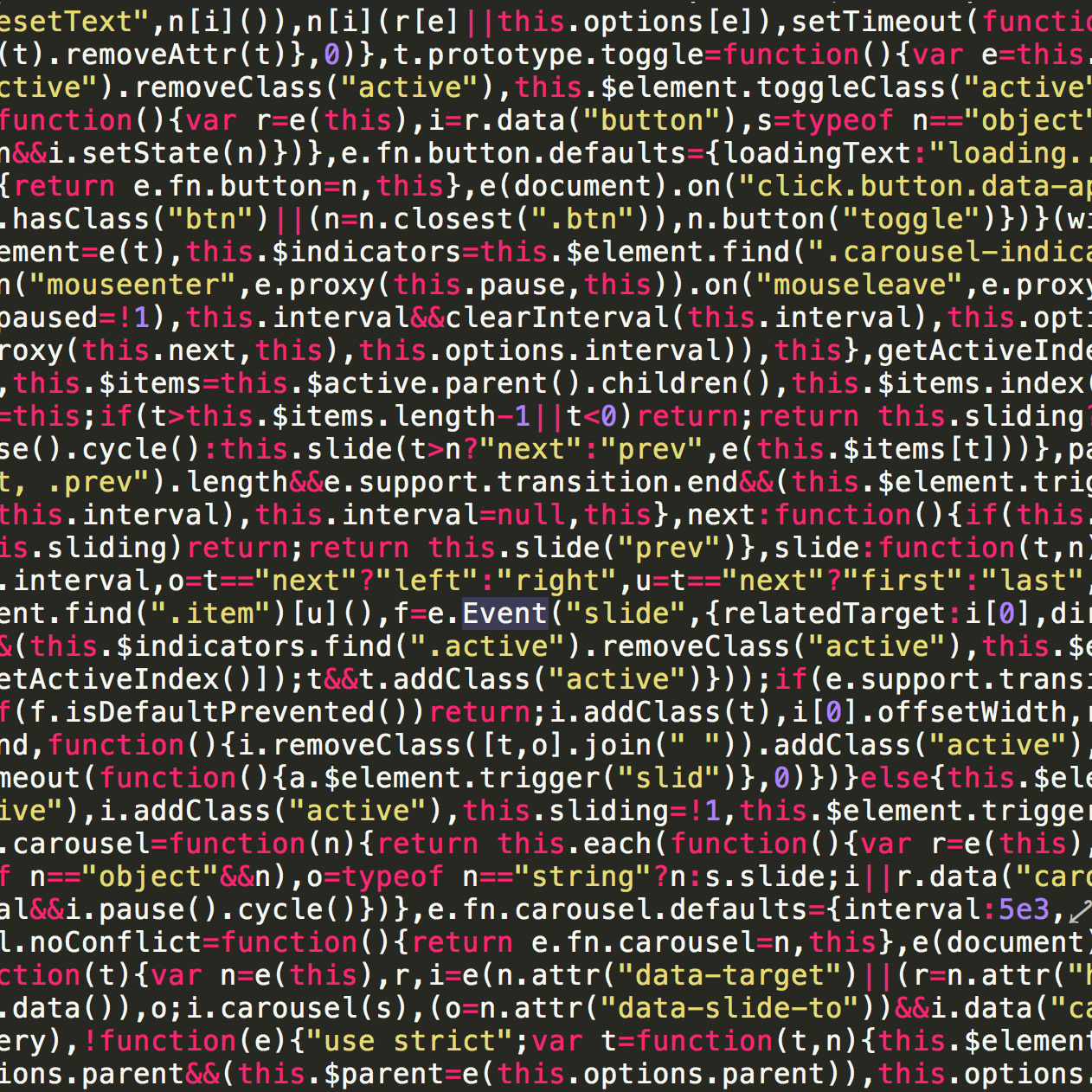
$ sudo vim /etc/ssh/sshd_config
In this configuration file, find and set these 4 directives:
PermitRootLogin no
ChallengeResponseAuthentication no
PasswordAuthentication no
UsePAM no
When you are finished, save your file and restart the SSHd server:
$ sudo service sshd restart
At this point, you should be able to log out and log back in again with no troubles. If you have any troubles, you still have that other window open and connected to the server so you can put the changes back the way they were in sshd_config and troubleshoot to see what happened.
Luck be with you!
Comments
Categories
- Stupid Stories 65
- On My Commute 31
- Computer Programming 21
- Italian Dual Citizenship 11
- Food 9
- Black Lives Do Matter 8
- The Beast 6
- Not So Stupid Stories 6
- Quick Projects 5
- Playing Out 5
- Movies I've Made 4
- Old Man Rants 3
- Scams 3
- The Robot Sbot 2
- Other's Music 2
- Film Projects 2
- Programming Tutorials 2
- Making Movies 2
- Rental Car Reviews 1
- My Original Music 1
- 3D Printing 1
- Ryvid Anthem 1